-Lightweight Cryptography for Resource Constrained IoT Device -Research on password optimization technology for IoT devices (8bit, 16bit, 32bit processors) -International standard IoT platform (oneM2M, L2M2M) security technology research -Mesh network security: IEEE 802.11s security Cryptography and Information Security
-Next Generation Post-Quantum Cryptography-
Optimization study of cryptographic algorithms (Simon, AES, LEA, ARIA, ECC, etc.) Optimal Implementation on Crypto-algorithms-
IoT platform security technology research (OneM2M, LwM2M, TLS, DTLS implementation and optimization research)-IoT
security chip technology research (Hardware Implementation of Crypto Hardware: FPGA implementation and ASIC implementation)[/vc_column_text ]
Development of security chips for the Internet of Things (AES, ARIA, LEA, ECC Cryptochip)
-Implementation of crypto optimization such as Simon, AES, LEA, ARIA, SHA256, ECC
-Research on side-channel attack prevention technology
-IoT protocol (CoAP, TLS, DTLS, etc.) security technology research
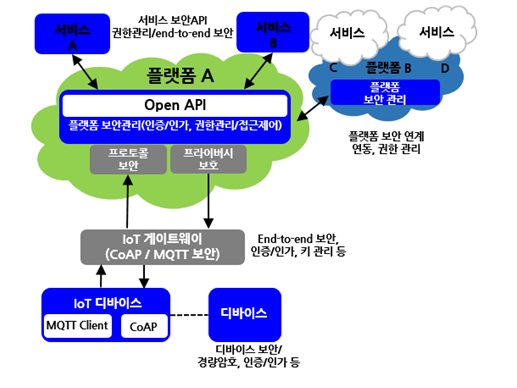
-Authentication, authorization, identification system technology research on IoT platformInternet of Things Platform Security Concept Map
-Lightweight encryption implementation technology
-Simon, AES, LEA, ARIA, ECC for IoT device
-OneM2M compatible device authentication protocol development
-WPAN security: IEEE 802.15.4 security
-CoAP, LWM2M security: IEEE 802.15.4 securityIoT Network Security Technology Concept Map
- Quantum cryptography research
-Next-generation post-Quantum Cryptography technology research
-LWE, LWE-Ring, Lattice-based post-quantum cryptography technology research – Post-Quantum cryptographic
speedup implementation technique research
 +82-51-510-1010
+82-51-510-1010


